Social engineering attacks have become a popular method used by threat actors to easily bypass authentication and authorization security protocols and gain access to a network.
 These attacks have increased significantly in the last 5 years becoming a lucrative business for hackers. Internal users pose the greatest security risk to an organization typically because they’re uneducated or unaware of the threat. Accidentally downloading an attachment or clicking a link to a website with malicious code can cost thousands in damages.
These attacks have increased significantly in the last 5 years becoming a lucrative business for hackers. Internal users pose the greatest security risk to an organization typically because they’re uneducated or unaware of the threat. Accidentally downloading an attachment or clicking a link to a website with malicious code can cost thousands in damages.
Note: This does not prove malicious intent. The user could be a victim of a social engineering attack.
The most common types of social engineering attacks include:
- Phishing emails
- Spear phishing
- Whaling
- Vishing
- Spam
- Pharming
- Tailgating
- Shoulder surfing
- Dumpster diving
Phishing Email
A phishing email scam is an online threat that appears to be from a legitimate user or business. These scams attempt to trick users into providing sensitive information such as a username and password, downloading or opening an application, or transferring money. Phishing relies on creating false trust, which is why threat actors will often send emails from familiar websites.
 When the user enters their credentials the bad guys log the username and password. The damage from a phishing attack can vary based on what information they have access to. For instance, a personal user may have their bank account siphoned or their identity stole. For a business, an attacker with access to an internal user’s computer can attempt to escalate their privileges and lock out system administrates.
When the user enters their credentials the bad guys log the username and password. The damage from a phishing attack can vary based on what information they have access to. For instance, a personal user may have their bank account siphoned or their identity stole. For a business, an attacker with access to an internal user’s computer can attempt to escalate their privileges and lock out system administrates.
Spear Phishing
Spear phishing is similar to phishing in that it attempts to trick a user. However, spear phishing attacks are designed to use personal information to get you to click a link. They will also sometimes use urgency or a risk of monetary value to bait their victims.

For example, the email from Bank of America to Amy B shows that someone has attempted to access her account and that the bank has locked it. In order for Amy to resolve the issue all she has to do is click on the link to reset her password. The threat actors are hoping Amy will be panicked about her money, clicks the link, and then gives them her login information.
Whaling
Whaling is a type of phishing attack that targets a high-profile business executive or manager with more critical information to lose. Whaling emails are different from other phishing attacks in that the emails and web pages serving the scam appear to be official.

Threat actors can easily use information from executives with information posted on the company’s website or social media to craft a unique message.

Vishing
Vishing, the combination of voice and phishing, is a phishing attack that takes place over the phone, typically a VoIP (Voice over IP) line. Threat actors are able to use tools specific to VoIP systems, thereby hacking their auto dialers to send robo messages from a spoofed VoIP address.
In 2018, nearly 48 billion robocalls were made in the U.S. in 2018, an increase of 57% over 30 billion in 2017, making vishing one of the fastest growing social engineering attack. In some cases threat actors will attempt to confuse you saying that your system is hacked and the password needs to be updated. Or that they need to request an urgent payment because they have some “information” on you. Sometimes, the bad guys will get clever by pretending to be friendly.
They may even ask questions like: what’s your dogs name, what street did you grow up on?, what was the color of your first car? Sound familiar?
Spam
Spam has been plaguing our inbox since the beginning. Spam is an attempt to send mass emails to large numbers of users. The emails are sometimes annoying solicitations or they can be scams or hoaxes.
You’re likely familiar with the popular Nigerian prince scam that’s responsible for millions in damages. In more recent history spam has been the primary delivery system for phishing emails carrying malware in email attachments and in hidden messages in images.
Pharming
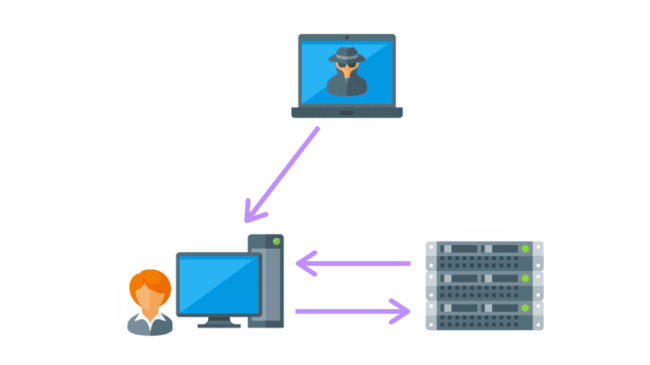
 Pharming is a type of social engineering attack that misdirects a user’s website’s traffic to a fake site. Similar to phishing, pharming occurs when code is installed on the computer that modifies the destination URL to the attacker’s. Pharming attacks typically take place by changing the hosts file on the computer or by exploiting a vulnerability in the DNS server software. Pharming can result in the loss of data, credit card information, or lead to identity loss.
Pharming is a type of social engineering attack that misdirects a user’s website’s traffic to a fake site. Similar to phishing, pharming occurs when code is installed on the computer that modifies the destination URL to the attacker’s. Pharming attacks typically take place by changing the hosts file on the computer or by exploiting a vulnerability in the DNS server software. Pharming can result in the loss of data, credit card information, or lead to identity loss.
Tailgating
 Not all social engineering attacks are done remotely or with the use of an electronic device. Tailgating is a simpler type of social engineering attack where the threat actor gains physical access to a facility by following a user through a security check point. Common courtesy is often how the threat actors break in.
Not all social engineering attacks are done remotely or with the use of an electronic device. Tailgating is a simpler type of social engineering attack where the threat actor gains physical access to a facility by following a user through a security check point. Common courtesy is often how the threat actors break in.
Holding a door for the person behind you, joining a crowd of people, and fooling authorized users into letting them in are all methods used. Businesses must have strict access control rules to prevent unauthorized individuals as well as employee training to quickly respond and report suspicious activity.
Shoulder Surfing
 Shoulder surfing is a type of social engineering that refers to obtaining personal or private information through direct observation. It’s very easy for a threat actor to casually glance over the shoulder of employee to view their monitor.
Shoulder surfing is a type of social engineering that refers to obtaining personal or private information through direct observation. It’s very easy for a threat actor to casually glance over the shoulder of employee to view their monitor.
Users should always be aware of their surroundings when using login names and passwords or when accessing sensitive data. This is especially true when using a computer, smartphone or ATM in a crowded area.
Dumpster Diving

Dumpster diving is social engineering reconnaissance. The threat actors are looking for any piece of information or clues they can get their hands on. They’re looking for account numbers, special events, contact names, numbers and more.
This information is then used in spear phishing and whaling attacks where personal identification information (PII) is used against the victim in an attempt to fool them. Dumpster diving is typically legal since trash does not have an owner, however, not all states abide to this law. It is also illegal to trespass on to someone’s property to then rummage through their trash.